Throughout 2021, CI Compass engaged with the U.S. National Science Foundation (NSF) Major Facilities (MFs) to learn about the many challenges that are inherent with the identity management practices these facilities use to manage security, privacy and access tiers within a facility’s cyberinfrastructure.
“NSF Major Facilities have their employees, users, as well as a lot of visiting members that utilize the MF capabilities including, sophisticated instruments, experimental platforms, physical infrastructure, cutting-edge computing resources, and data,” said Erik Scott, CI Compass team member, leader of the CI Compass Identity Management (IdM) Working Group (WG), and senior research software developer at the Renaissance Computing Institute at the University of North Carolina – Chapel Hill (RENCI). “Major Facilities may also have scientists and users who come from industries and organizations that are not really strictly considered academic. That alone complicates some things.”
In addition, students may rotate in and out of the Major Facilities, MF users may change affiliations, faculty may leave and return, and visiting scientists may need access to their own research but have other restricted accesses.
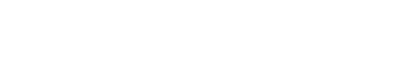
To address these challenges, the CI Compass IdM WG was created by members from CI Compass and Trusted CI, a partner project leading the development of an NSF Cybersecurity Ecosystem that enables trustworthy science. Together, this working group created a living document, “The Federated Identity Management Cookbook.” This “cookbook” will stand as an ever-evolving guide on identity management for the NSF Major Facilities as needs, regulations, technologies, tools, and programs change over time.
The MFs’ needs for identity management are rooted in the need to manage privacy, security and access tiers within their systems. On the user end, identity management appears as the login feature used to access data, services, and communications. These can have a multi-factor login process. On the back-end of the system are layers of programming and security features to keep data safe.
MFs come in many staffing sizes, some with minimal staff members maintaining the facility, and some with over 1,000 employees. “A larger facility will have many visiting scientists and students at different times and providing username and password management for an organization like that would be similar to the requirements for a medium sized university at that point,” Scott said. “There is a lot of subtlety to it.”
Many of the research facilities that are established have been working with older software and hardware on-site. The costs, or sheer size of the task, to update or rebuild identity management systems may appear to be an obstacle to facilities. Each facility’s needs may be unique to their area of study and users. Using appropriate programs and building customizable and manageable backends for identity management systems will continue to be a challenge for MFs going forward.
Scott and the IdM WG hope to address some of those concerns with the “Cookbook.” Within this reference guide are an overview of the current IdM protocols and tools, and best-practice solutions to challenges that both brand new and established research facilities may need to consider as they build or evolve their identity management infrastructure.
“I’m pleased with the cookbook’s emphasis on federated identity, because federating with the researcher’s existing, strong campus identity, with associated security credentials, has significant security and usability benefits when compared to the alternatives,” said Jim Basney, Director of Trusted CI. “As a living document, this cookbook represents the output of the IdM WG on an ongoing basis, with participation by CI Compass, Trusted CI, the NSF Major Facilities, and the broader community, including members and representatives of the InCommon federation.”
“The Federated Identity Management Cookbook is a product of our successful collaboration with Trusted CI, the NSF Cybersecurity Center of Excellence (CoE). Working together with another NSF CI CoE, we were able to produce a living document that will help guide the NSF Major Facilities and other projects relying on modern cyberinfrastructure as they design, implement and upgrade their identity management systems,” said Ewa Deelman, Principal Investigator for CI Compass.
The document is available in the CI Compass Resource Library and on Zenodo. As IdM tools, technologies and best-practice solutions evolve, CI Compass plans to update and release subsequent versions of the Cookbook. If you have comments on the Cookbook or want to join the IdM Topical Working Group, please send an email to contact@ci-compass.org.
About CI Compass
CI Compass is funded by the NSF Office of Advanced Cyberinfrastructure in the Directorate for Computer and Information Science and Engineering under grant number 2127548. Its participating research institutions include the University of Southern California, Indiana University, Texas Tech University, the University of North Carolina at Chapel Hill, the University of Notre Dame, and the University of Utah.
To learn more about CI Compass, please visit ci-compass.org.
About Trusted CI
Trusted CI is supported by the National Science Foundation under Grant #1920430. As the National Science Foundation Cybersecurity Center of Excellence, Trusted CI draws on expertise from multiple internationally recognized institutions, including Indiana University, the University of Illinois, the University of Wisconsin-Madison, the Pittsburgh Supercomputing Center, and Berkeley Lab.
To learn more about Trusted CI, please visit trustedci.org.
Contact:
Christina Clark, Research Communications Specialist
CI Compass / Notre Dame Research / University of Notre Dame
cclark26@nd.edu / 574.631.2665
ci-compass.org / @cicompass